Below is the command to check that a private key which we have generated (ex: domain.key) is a valid key or not $ openssl rsa -check -in domain.key If the private key is encrypted, you will be prompted to enter the pass phrase. Upon the successful entry, the unencrypted key will be the output on the terminal. With openssl, if your private key is in the file idrsa, then openssl rsa -text -noout -in idrsa will print the private key contents, and the first line of output contains the modulus size in bits. Public tableau gallery. If the key is protected by a passphrase you will have to enter that passphrase, of course. OpenSSL Command to Generate Private Key openssl genrsa -out yourdomain.key 2048 OpenSSL Command to Check your Private Key openssl rsa -in privateKey.key -check OpenSSL Command to Generate CSR. If you have generated Private Key: openssl req -new -key yourdomain.key -out yourdomain.csr. Once you execute this command, you'll be asked additional. Openssl req -newkey rsa:2048 -nodes -keyout domain.key-x509 -days 365 -out domain.crt The –days parameter is set to 365, meaning that the certificate is valid for the next 365 days. The x509 parameter indicates that this will be a self-signed certificate.
Skip to main contentEncrypt and decrypt files to public keys via the OpenSSL Command Line
Published: 25-10-2018 | Author: Remy van Elst | Text only version of this article
Openssl Rsa Key Generation
❗ This post is over two years old. It may no longer be up to date. Opinions may have changed.
Table of Contents
This small tutorial will show you how to use the openssl command line to encryptand decrypt a file using a public key. We will first generate a random key,encrypt that random key against the public key of the other person and use thatrandom key to encrypt the actual file with using symmetric encryption.
Consider sponsoring me on Github. It means the world to me if you show your appreciation and you'll help pay the server costs.
You can also sponsor me by getting a Digital Ocean VPS. With this referral link you'll get $100 credit for 60 days.
Because of how the RSA algorithm works it is not possible to encrypt largefiles. If you create a key of n bits, then the file you want to encrypt mustnot larger than (n minus 11) bits. The most effective use of RSA crypto is toencrypt a random generated password, then encrypt the file with the passwordusing symmetric crypto. If the file is larger then the key size the encryptioncommand will fail:
We generate a random file and use that as the key to encrypt the large file withsymmetric crypto. That random file acts as the password so to say. We encryptthe large file with the small password file as password. Then we send theencrypted file and the encrypted key to the other party and then can decrypt thekey with their public key, the use that key to decrypt the large file.
The following commands are relevant when you work with RSA keys:
Ssh Rsa Key
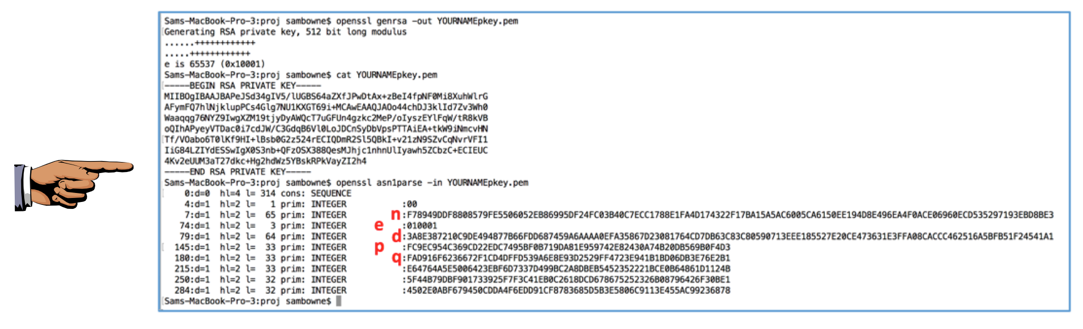
openssl genrsa: Generates an RSA private keys.openssl rsa: Manage RSA private keys (includes generating a public key from it).openssl rsautl: Encrypt and decrypt files with RSA keys.
Openssl Rsa Key Pair
The key is just a string of random bytes. We use a base64 encoded string of 128bytes, which is 175 characters. Since 175 characters is 1400 bits, even a smallRSA key will be able to encrypt it.
Get the public key
Let the other party send you a certificate or their public key. If they send toa certificate you can extract the public key using this command:
Generate the random password file
Use the following command to generate the random key:
Do this every time you encrypt a file. Use a new key every time!
Update 25-10-2018
The key format is HEX because the base64 format adds newlines. The -passargument later on only takes the first line of the file, so the full key is notused. (Thanks Ken Larson for pointing this to me)
Encrypt the file with the random key
Use the following command to encrypt the large file with the random key:
The file size doesn't grows that much:
It's encrypted however:
Openssl Rsa Key To Pem
Encrypt the random key with the public keyfile
Use the following command to encrypt the random keyfile with the other personspublic key:
You can safely send the key.bin.enc and the largefile.pdf.enc to the otherparty.
You might want to sign the two files with your public key as well.
Decrypt the random key with our private key file
If you want to decrypt a file encrypted with this setup, use the followingcommand with your privte key (beloning to the pubkey the random key was cryptedto) to decrypt the random key:
This will result in the decrypted random key we encrypted the file in.
Decrypt the large file with the random key
Once you have the random key, you can decrypt the encrypted file with thedecrypted key:
This will result in the decrypted large file.
Tags: ca, certificate, decrypt, encrypt, openssl, pki, ssl, tls, tutorials